
The CertGraveyard was officially launched in January 2025 but hasn’t been featured in a blog post. This post will explain what it is, how you can leverage it for your own cyber defense, and how you can contribute.
Note: The CertGraveyard had a different name for a while, but I had to change due to being too similar to an existing trademark. The name “CertGraveyard” is intentionally a little “cheesy” but in my opinion, it is the right amount of silly and serious.
Ignorance or blind trust
In 2021, when I was looking to raise detection rates for SolarMarker malware, I noticed that the malware was signed with a code-signing certificate. It struck me as wrong that they could abuse this system. I reported it for revocation. The actor obtained a new cert. I reported the new cert. They acquired yet another. This happened 100 times. Since then, I’ve been involved in the reporting of more than 2,000 certificates across many malware families.
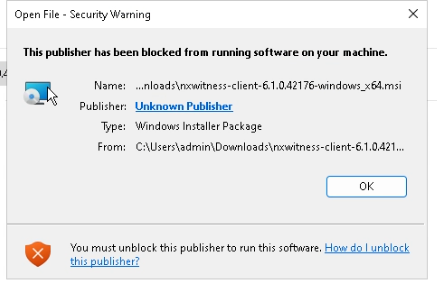
As I’ve talked to people over the years, most people suspected or knew there was a problem around code-signing certificates but very few have investigated to understand the size of the problem. For years, very few people have reported certificates to be revoked. Neither of these outcomes are great as it comes to code-signing. Code-signing is a system of trust.
This is where the CertGraveyard comes in.
The final resting place for certificates
The CertGraveyard’s primary objective is to mitigate and stop damage caused by signed malware.
The CertGraveyard is a public record of code-signing abuse… except we don’t just document the abuse: we report the certificates. Reporting the certificates give the Certificate Authorities (CA) who issue them the chance to respond to the abuse. Without reporting, the CAs don’t have this opportunity: For the most part, CAs don’t scour the internet to find abuse, but rely on reports.
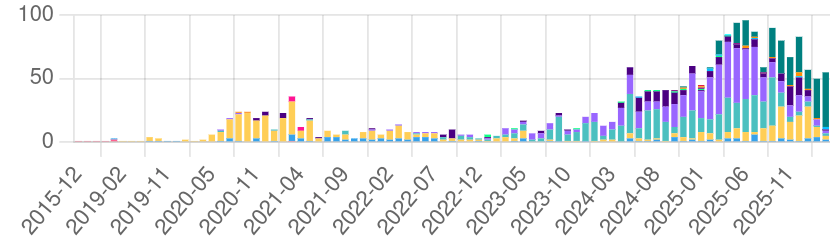
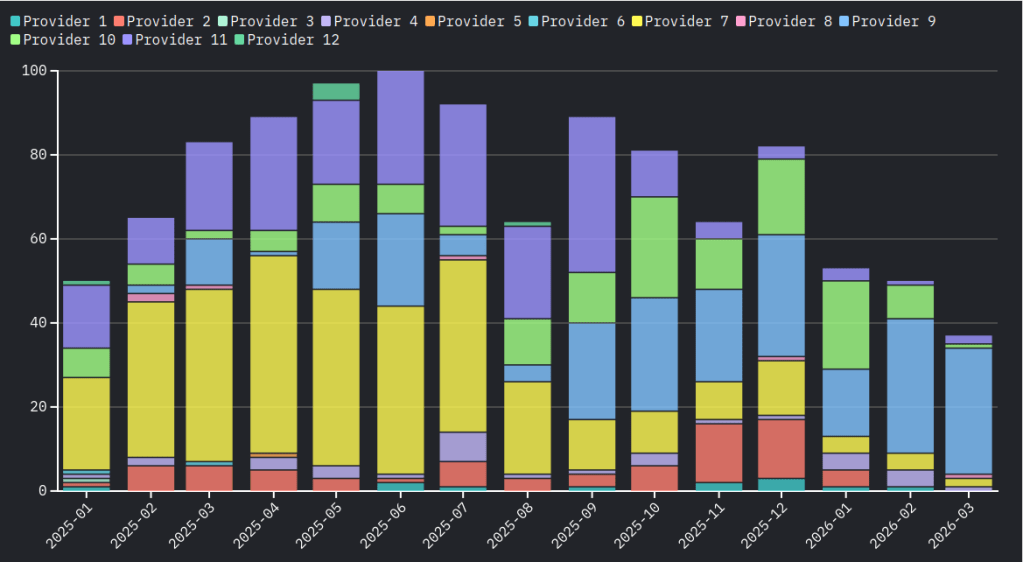
The database serves as a record to document which malware families and which certificate providers are seeing abuse. There is no other public record of this. Unlike SSL/TLS certificates, there is no code-signing transparency log. Even if there was—it wouldn’t provide context around the abuse and link it back to malware campaigns. With the CertGraveyard, we are able to be vendor agnostic and use our database to track malware families, connections between those families, and observe trends over time to help us better understand the certificate reselling ecosystem.
Reporting the certificates themselves also has real results. CAs respond to reports within 0 to 24 hours to revoke a certificate and when revoked, the status of the certificate will negatively impact the malware campaign since it cannot be used to sign new malware and is no longer trusted by Windows.
Reporting
The CertGraveyard allows anyone to report an abused code-signing certificate using our web form. All submissions are reviewed and details are submitted to the appropriate Certificate Authority for revocation. This helps users to not worry about finding the right contact nor needing to spend excessive time writing up details.
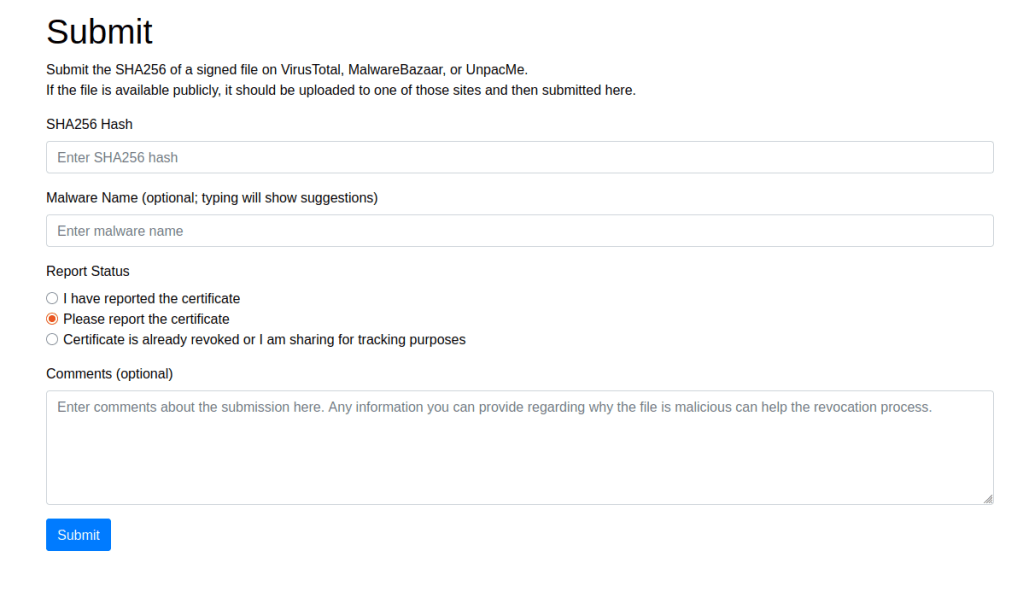
In addition to just reporting through the web form, those who want to be move engaged in the process have options:
Do it yourself option
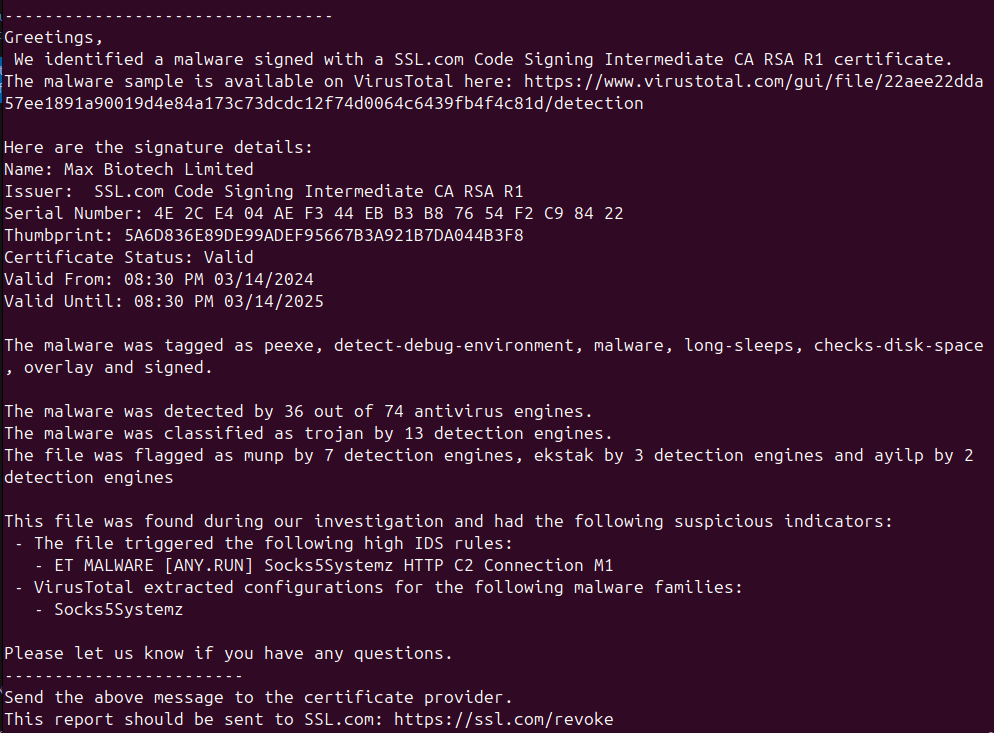
First, users can report using certReport and a certGraveyard API key. CertReport generates a report and instructs the user where to send it. We use this tool ourselves for every report. The CertGraveyard API key allows you to submit the certificate details to the CertGraveyard: the whole process allows you to fully engage in the reporting process and contribute to the community. (An API key can be obtained from the profile page, once one logs in at CertGraveyard.org )
Do it together option
Second, we welcome others to contribute to malware analysis in our Discord server. The server acts as a central hub for communication and automation. Automated workflows surface information about signed files for investigation. This makes it an easy place to know what needs to be reviewed, what has been seen, and discuss the malware or the analysis of the files.
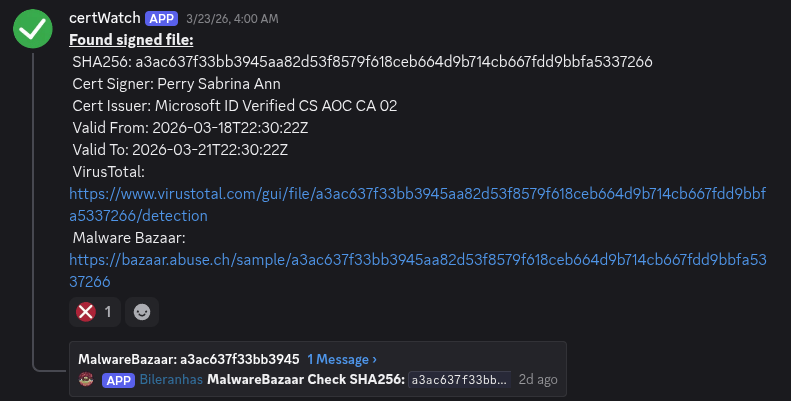
We currently see an average of 80 certificates needing revoked each month. If you’re interested in learning malware triage, digging your hands into malware that may be low detection and new, and contribute to raising the detection of these signed malware, we encourage you to join.
Prevention: dead for real
The CertGraveyard has partnered with MagicSword.io to make it easy to preemptively block signed files. MagicSword had already built out their product to block other software, including abused remote management and monitoring (RMM) tools and signed drivers; so leveraging the CertGraveyard database to block signed malware was a natural choice. Essentially, MagicSword does this by managing Windows Defender Application Control policies for you, augmenting them with their intelligence sources.
MagicSword is the only solution I’ve found to meaningfully block signed files at scale. To my awareness, the other options for cyber defense up to this point were primarily centered around hunting for activity that already happened. So MagicSword’s ability to block the files based on their certificates is a significant advantage for defenders.
Note: The link in this section is an affiliate link: if you use my link and choose to pay for MagicSword, it supports the CertGraveyard.
Our partners
In the last year, the CertGraveyard has received a lot of support for partners that we want to recognize here.
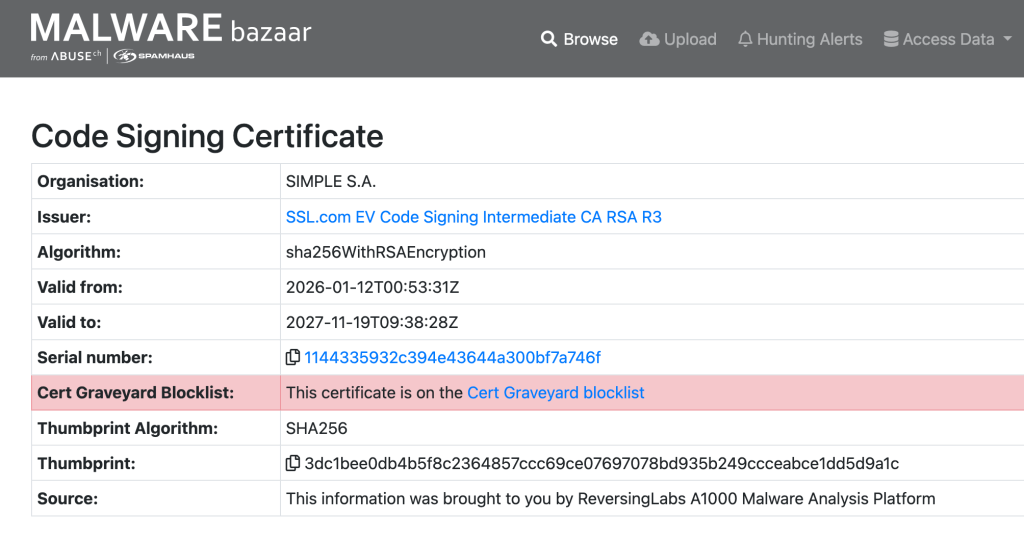
AbuseCH is one of our major sources of data. We use MalwareBazaar’s API to find signed files to triage. We leverage MalwareBazaar to review sandbox analysis results to help us make a determination if a file is malicious and what malware family is involved. They have also integrated an API request to the CertGraveyard to display when a signed file is within our database.
UnpacMe is a source of data too. They’ve generously allowed us to query their database via their API. We use their analysis reports to gain a better depth of understanding to the malware we see. Their YARA scanning allows us to test rules for additional malware hunting and allows us to easily test against goodware.
Malcat is a major tool we use for analysis. Malcat has parsers for every file type we come across, allowing us to do easy manual analysis. We’ve also built Malcat scripting into our analysis pipeline: all certificate data from EXE, MSI, MSIX, or other files, are extracted using Malcat. Malcat’s MCP server is used in our AI/LLM lab environment for analyzing malware.
MagicSword makes the CertGraveyard practical. While the certificate revocations have important impacts, it doesn’t stop the malware already deployed. So with MagicSword, the CertGraveyard is no longer just data in a database, but the records now have even greater impact.
If you or your org are interested in partnering or helping us in our mission, please reach out to me via “Squiblydoo at pm.me”.
Special thanks
Thanks to others who have made meaningful projects leveraging the CertGraveyard, such as doing your own threat hunting or YARA rules. Your use of the database gives encouragement in light of the endless onslaught of code-signing abuse.
Thanks to the Certificate Authorities for handling hundreds to thousands of reports over the last five years. There are still more to come.
